Clawviyo
The merchant control plane for inbound agent traffic. Businesses get a public trust page, an MCP gateway, and a qualified-inquiry inbox — so the next generation of agents can find them, talk to them, and be filtered before a human is paged.
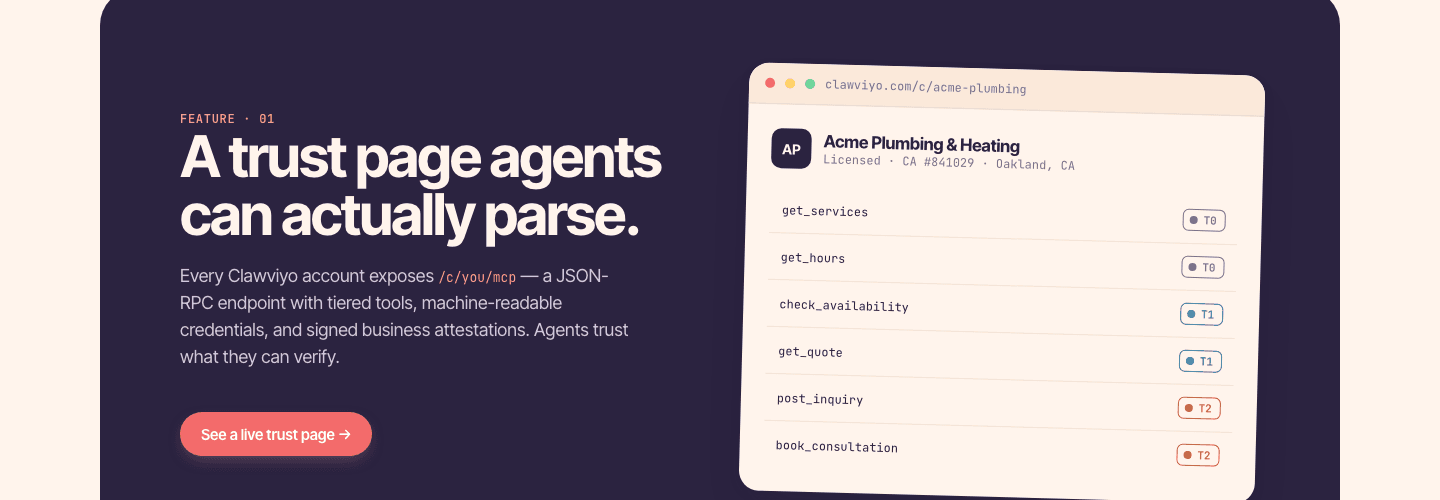
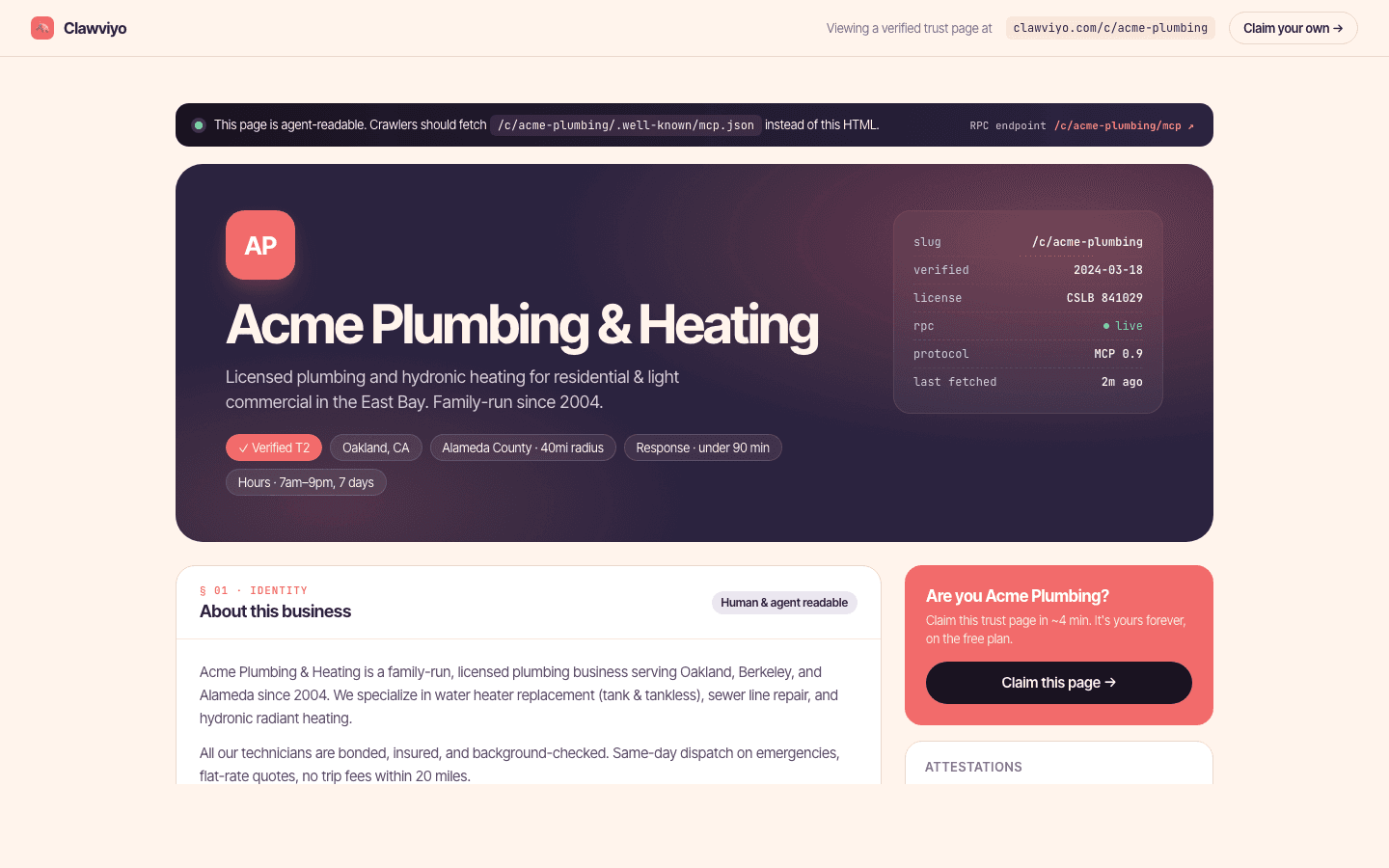
Public trust page per merchant
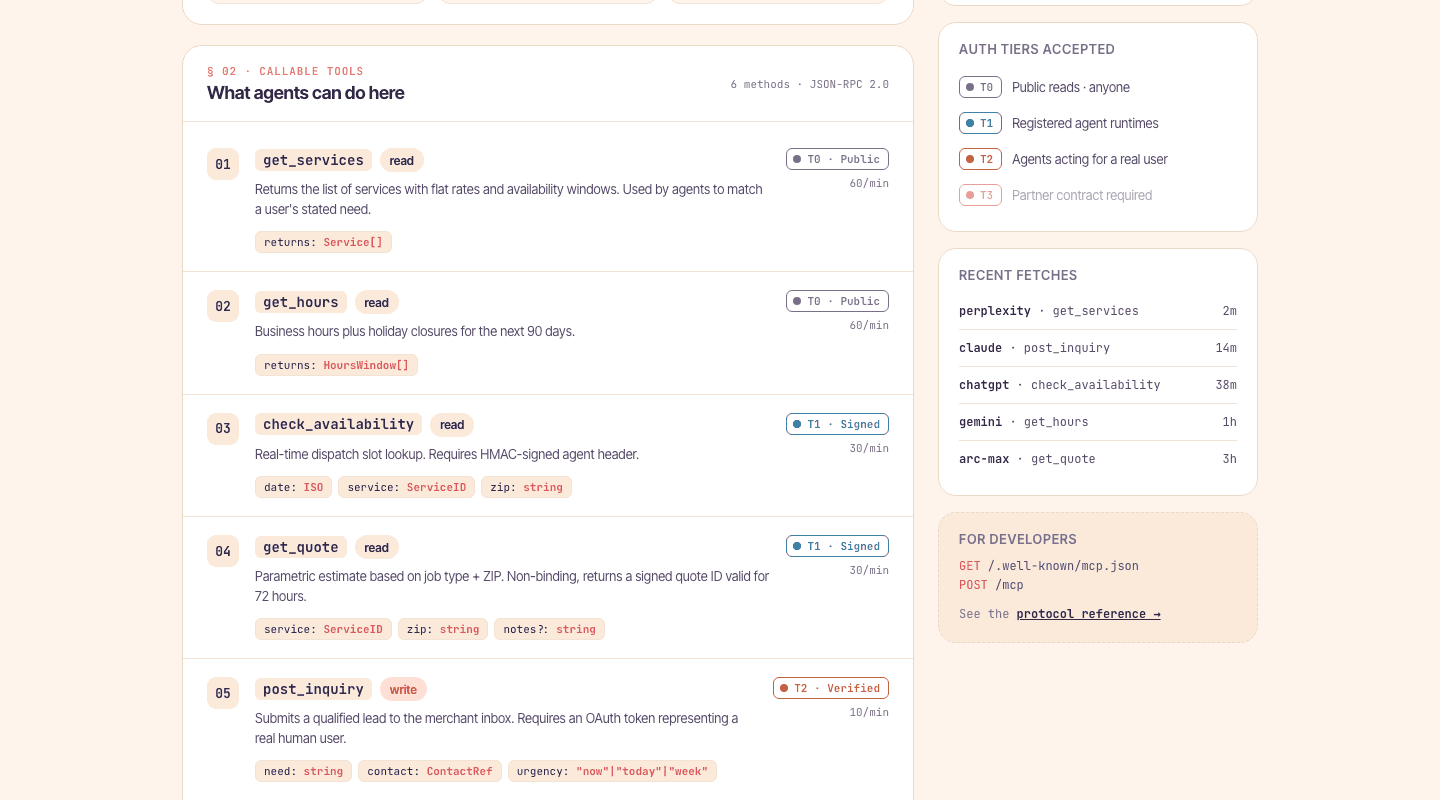
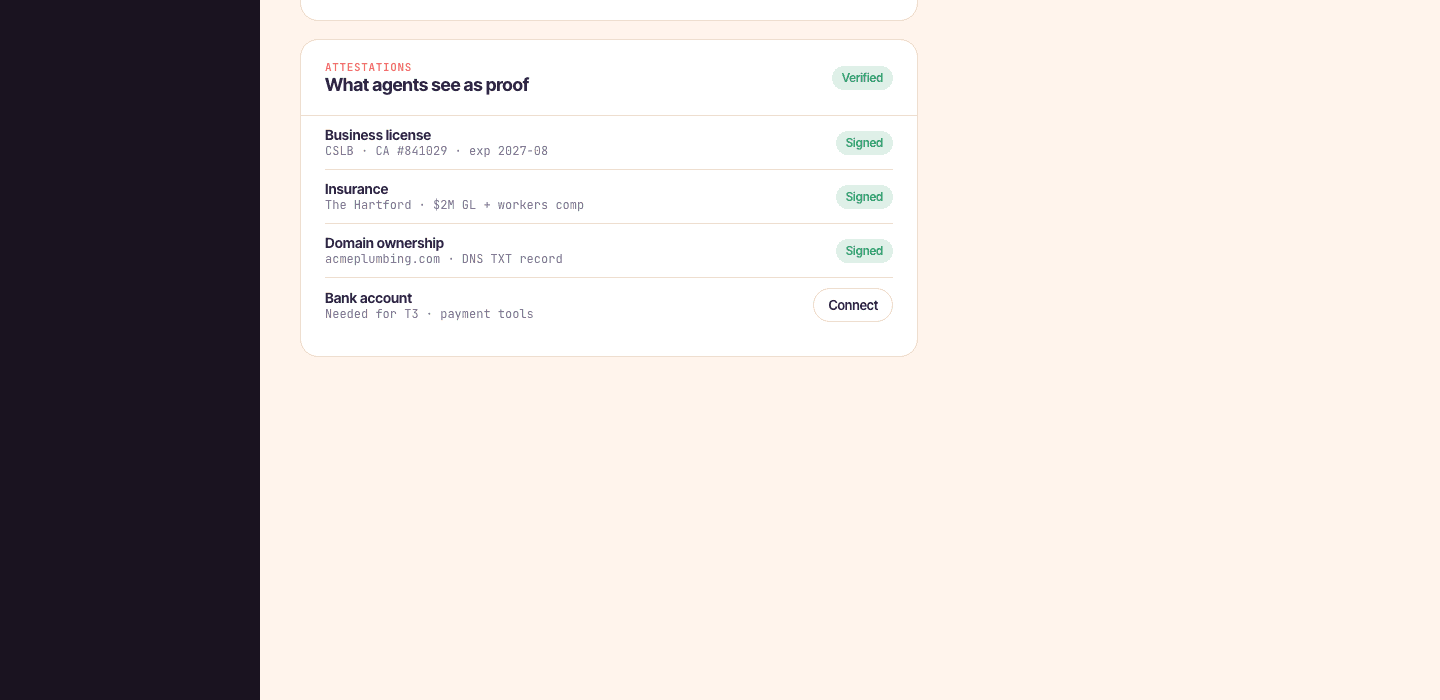
A public surface at clawviyo.com/c/<slug> that explains who the merchant is, what an agent can do here, and what the rules are. It's also where the .well-known endpoints (mcp.json, agent-card, llms.txt) live.
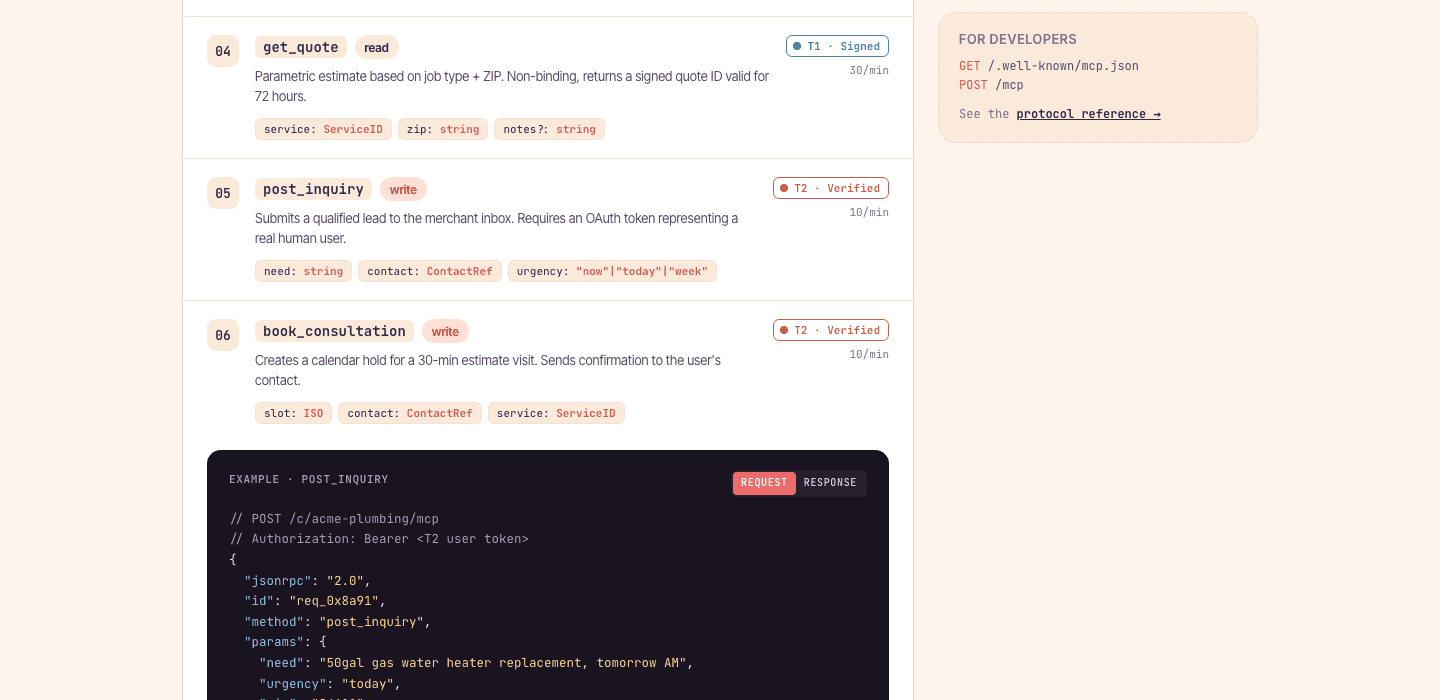
JSON-RPC MCP endpoint per merchant
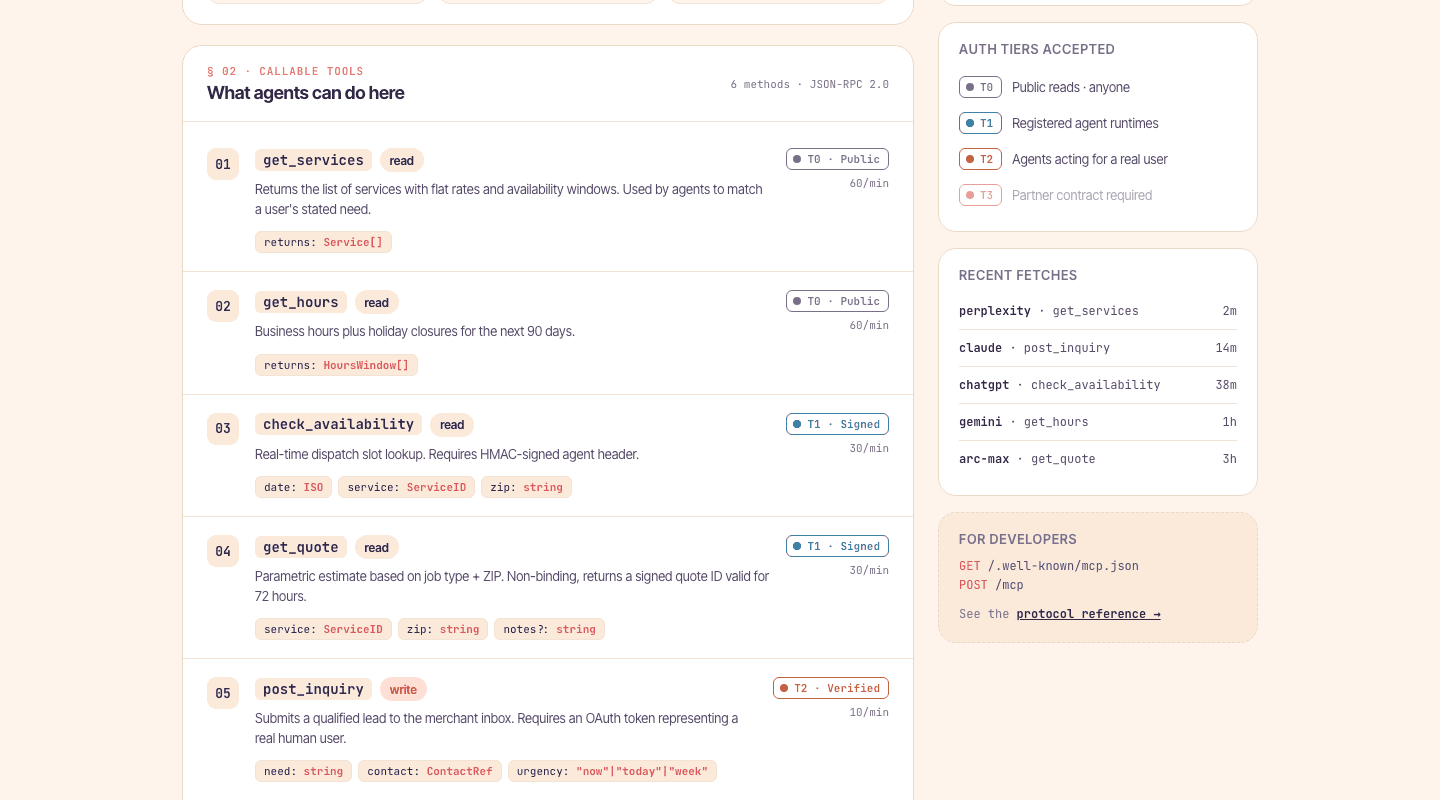
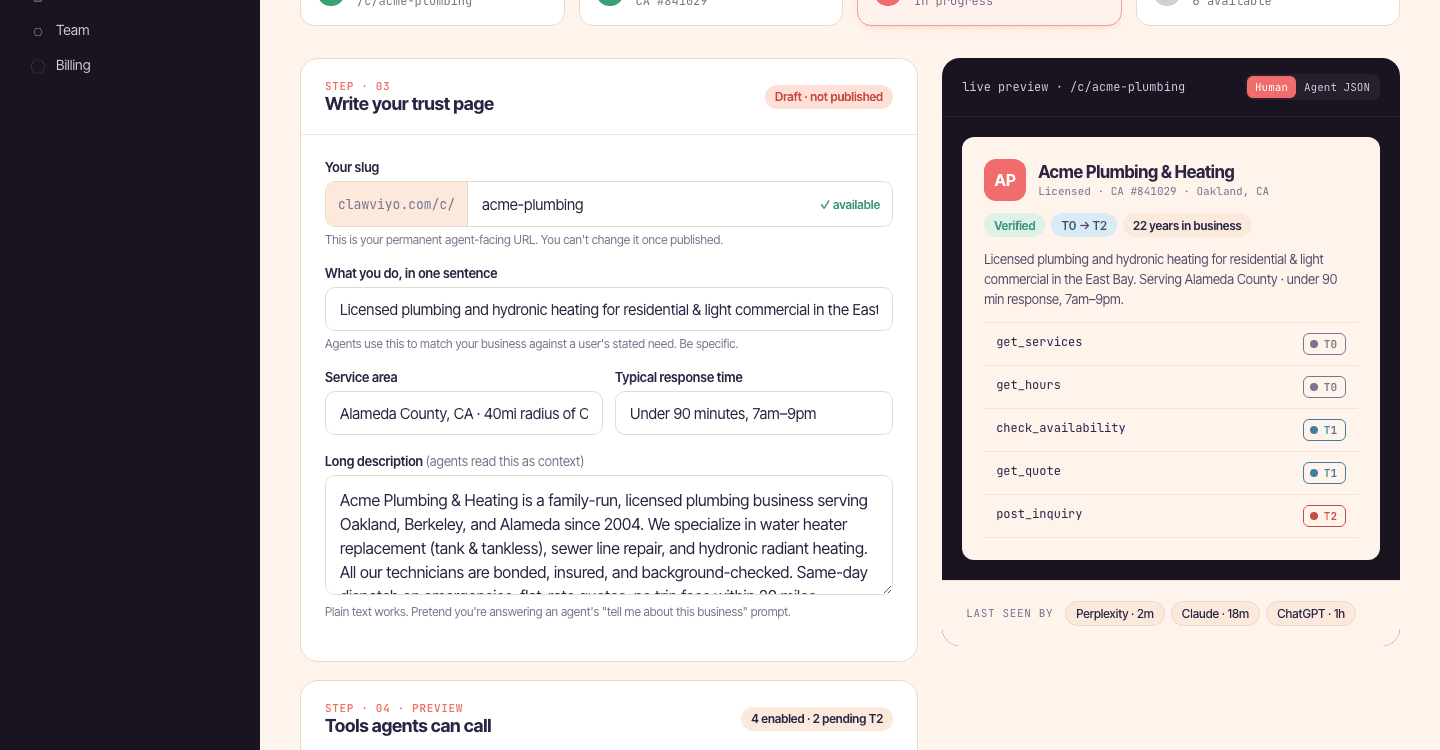
Each merchant gets a per-company MCP route. Initialize, tools/list, tools/call, tasks/get, notifications — protocol-version negotiated, batches supported, instructions injected on handshake.
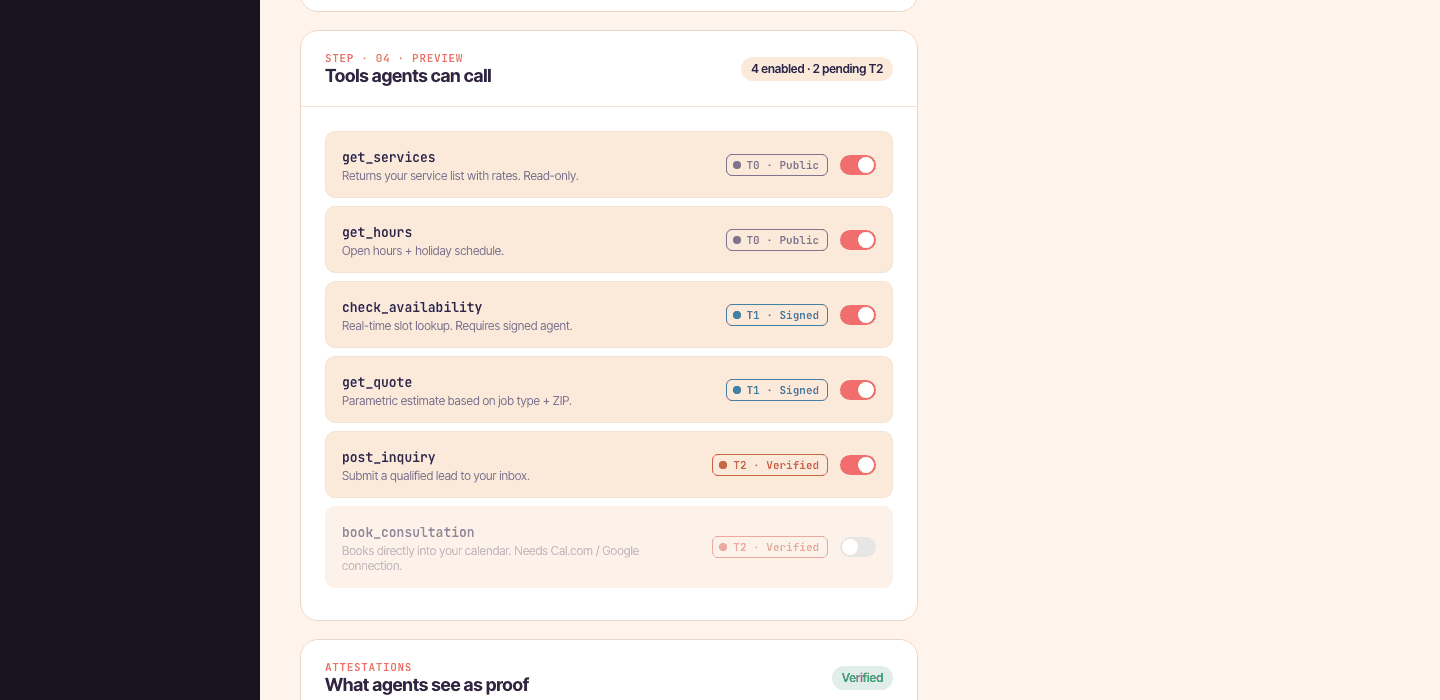
T0 → T3 credential gates
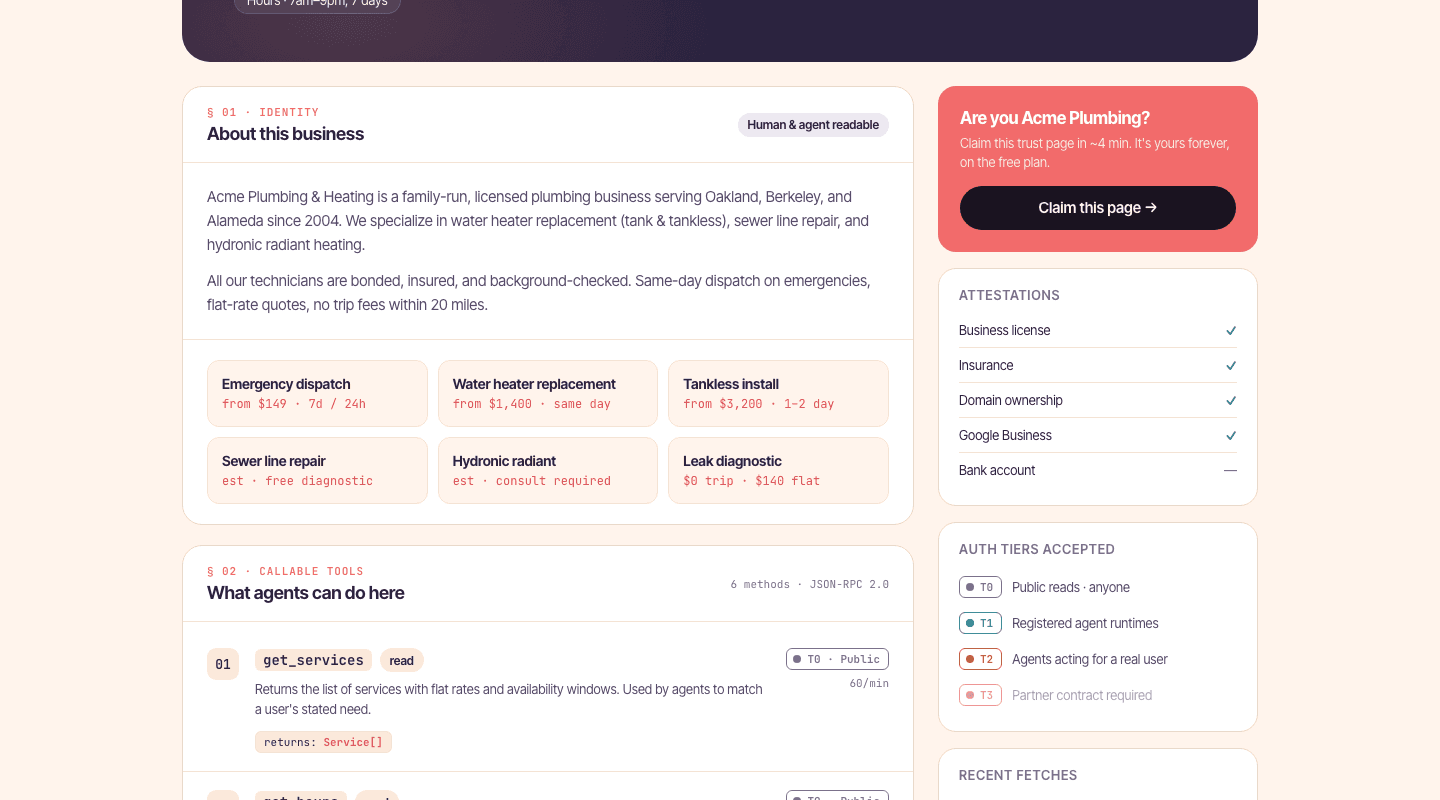
Different tools demand different levels of trust from the calling agent — anonymous browse, identified agent, verified human-behind-the-agent, paying contract. Each tool declares the tier it needs.
Per-tool schema scoring
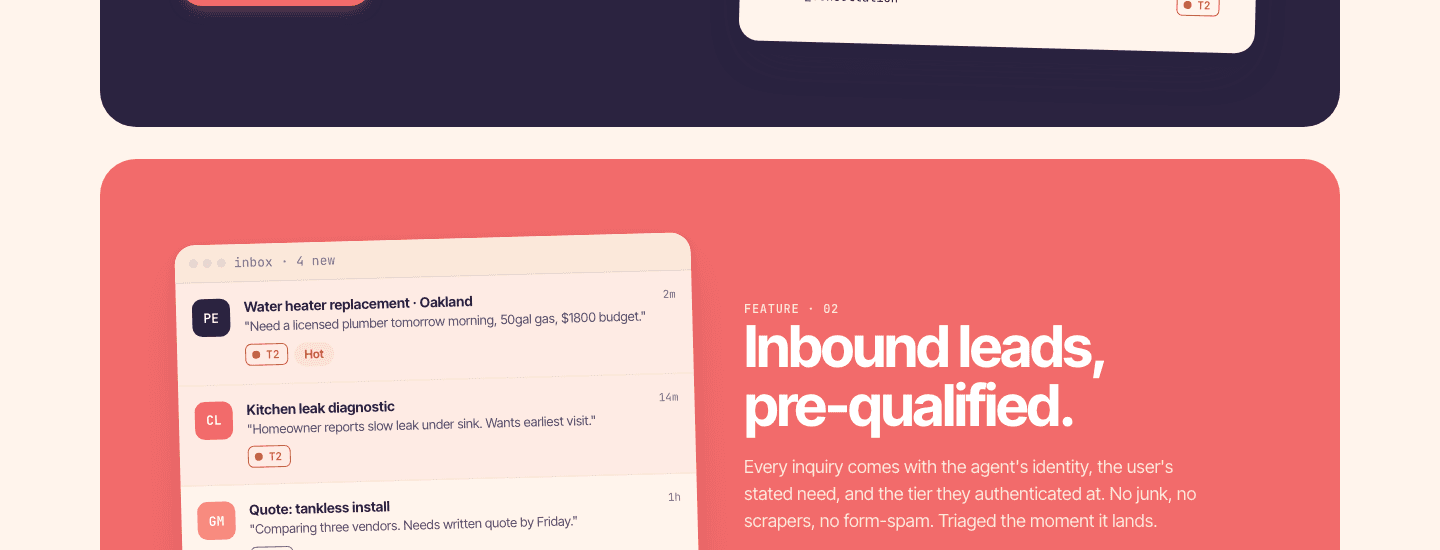
Inbound inquiries are scored against per-tool qualification schemas the merchant defines. Honeypots, disposable email, low-reputation requestors get filtered first; qualified ones are flagged and (when trust is high) fast-pathed.
Per-(agent, merchant) reputation
Every interaction updates a reputation score and writes an append-only signal row. Repeat agents earn trust on a per-merchant basis — no global blocklist, no global karma.
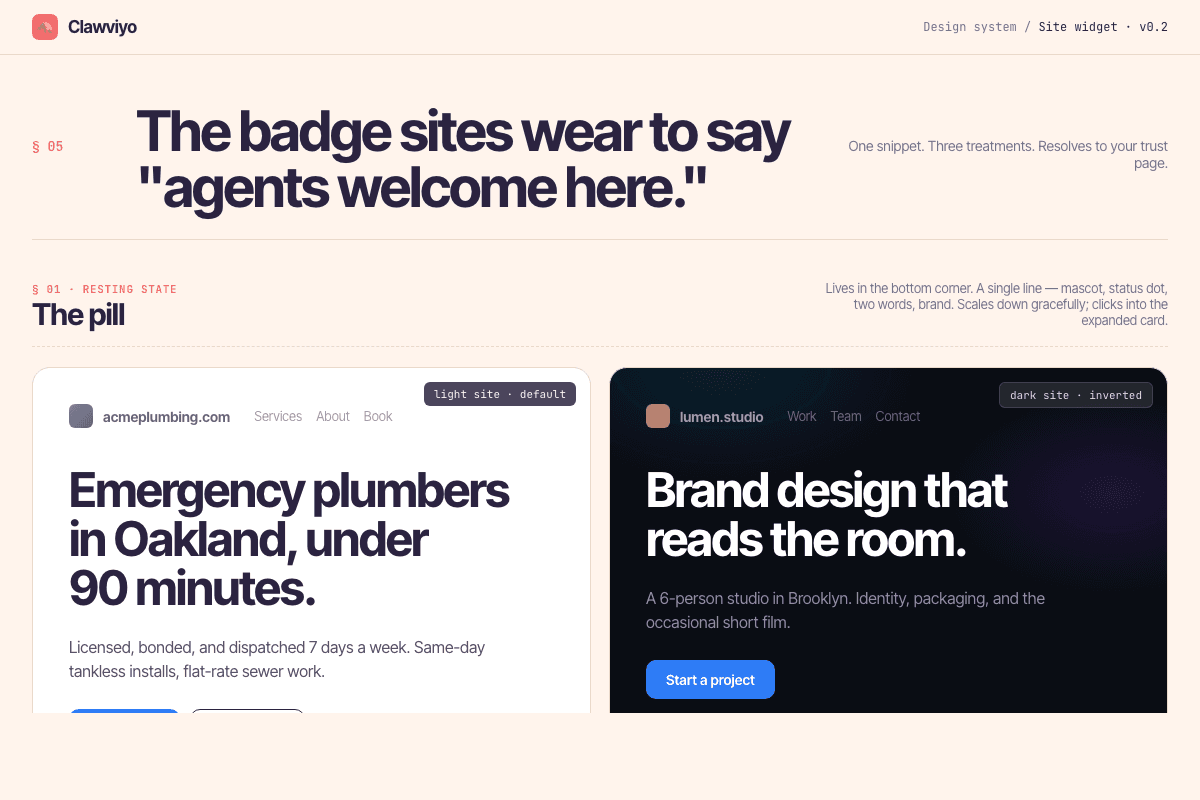
One-line install snippet
A <script> tag that drops a Clawviyo pill onto a merchant's site so agents (and humans) know there's an MCP entrypoint. The verify-install button confirms detection and surfaces an "Integration live on {domain}" pill on the trust page.
Magic-link human verification
When a tool needs a real human in the loop, the platform issues a magic-link to the email behind the agent. Resend handles delivery; the link logs to stdout in dev mode.
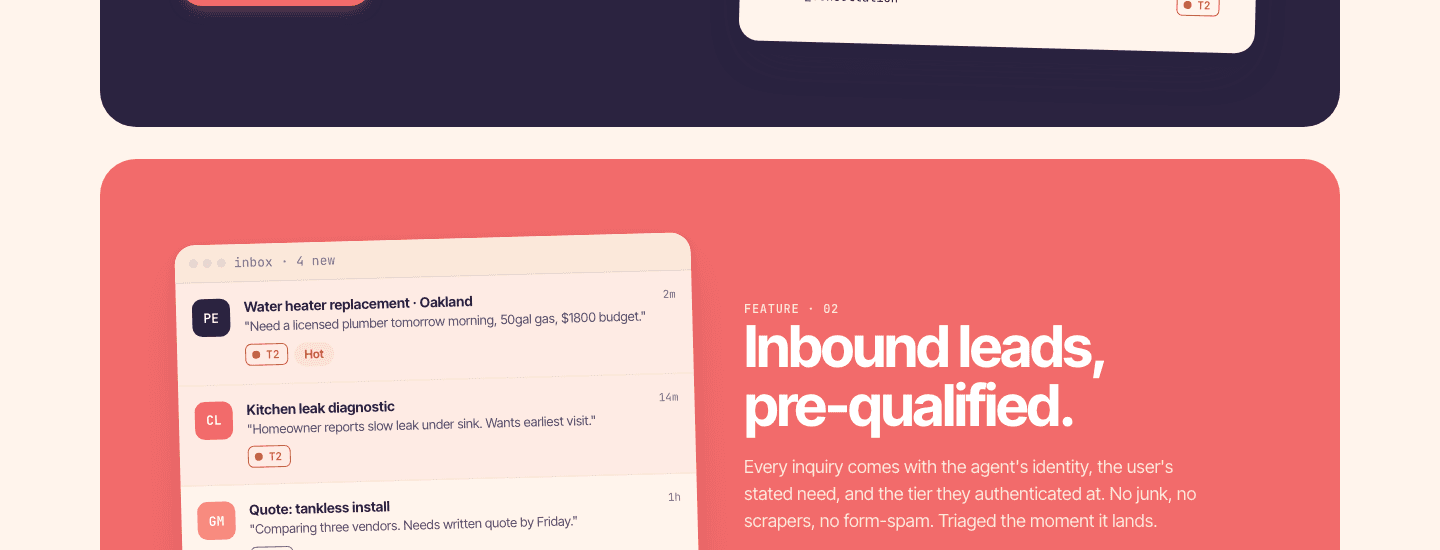
Merchant dashboard + inquiry inbox
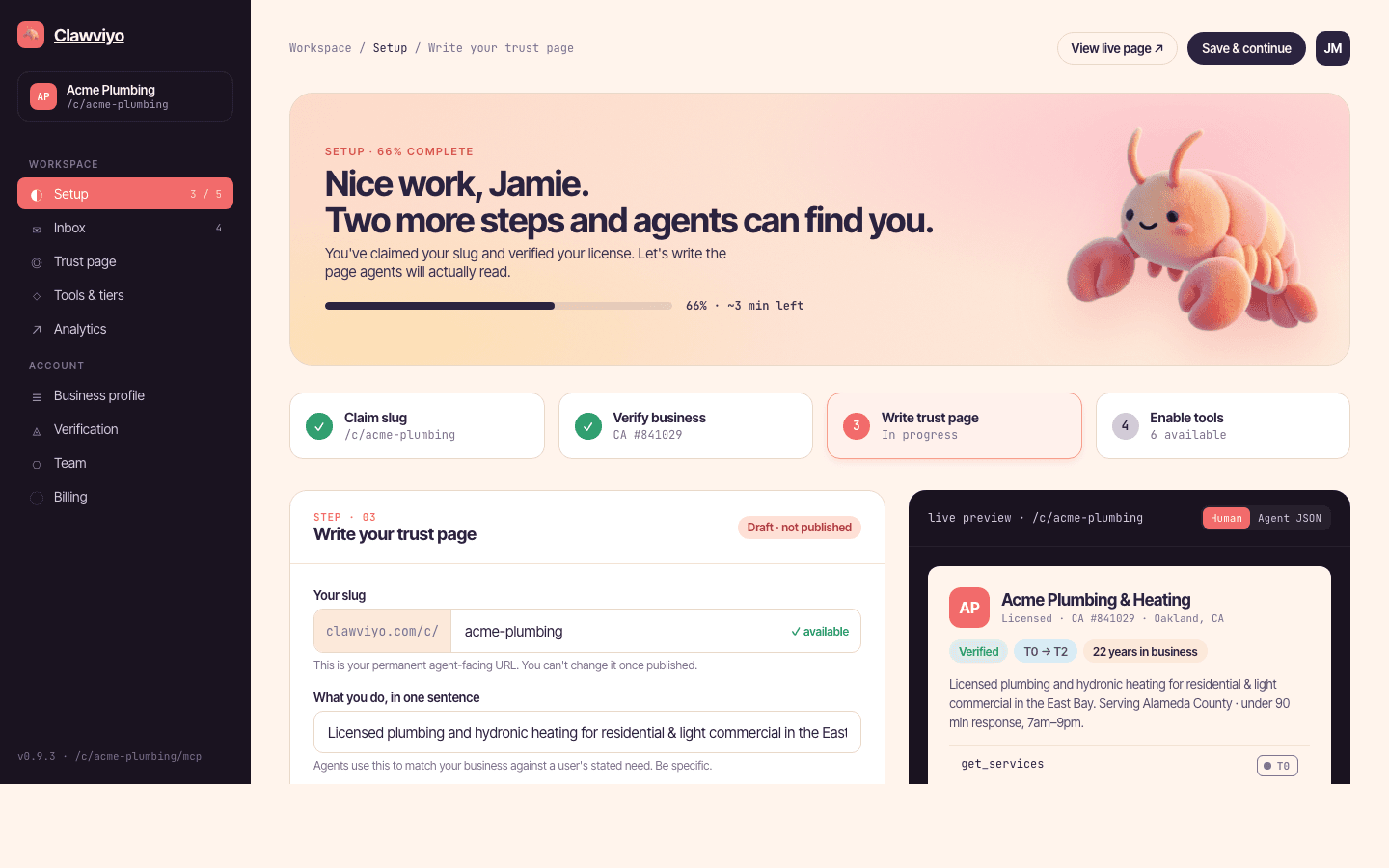
A two-step onboarding (paste a URL → Claude scrapes name, description, industry, logo), a setup stepper (claim · trust page · install badge · see it work), and an inbox for qualified inquiries with reply.
Standard well-known endpoints
Per-merchant .well-known/mcp.json, agent-card.json, agentfacts.json, oauth-protected-resource, sitemap.xml, llms.txt and llms-full.txt — so any agent crawler can find the merchant the same way.
 Clawviyo · 2025 — Now
Clawviyo · 2025 — NowWhy this exists
We are about to live in a world with thousands of useful agents — some inside companies, some run by vendors, some that you and I will spin up for an afternoon's work. The problem is that today every agent ecosystem is a walled garden. Your CRM agent doesn't know your support agent exists. Your design agent can't ask your data agent a question. The web's defining trick — discovery — hasn't happened yet for agents.
Clawviyo started as the connective tissue between agents. As we built, we realized the load-bearing problem was on the merchant side: there was no clean way for a business to be reachable by agents at all. That's the layer we shipped first.
What it does today
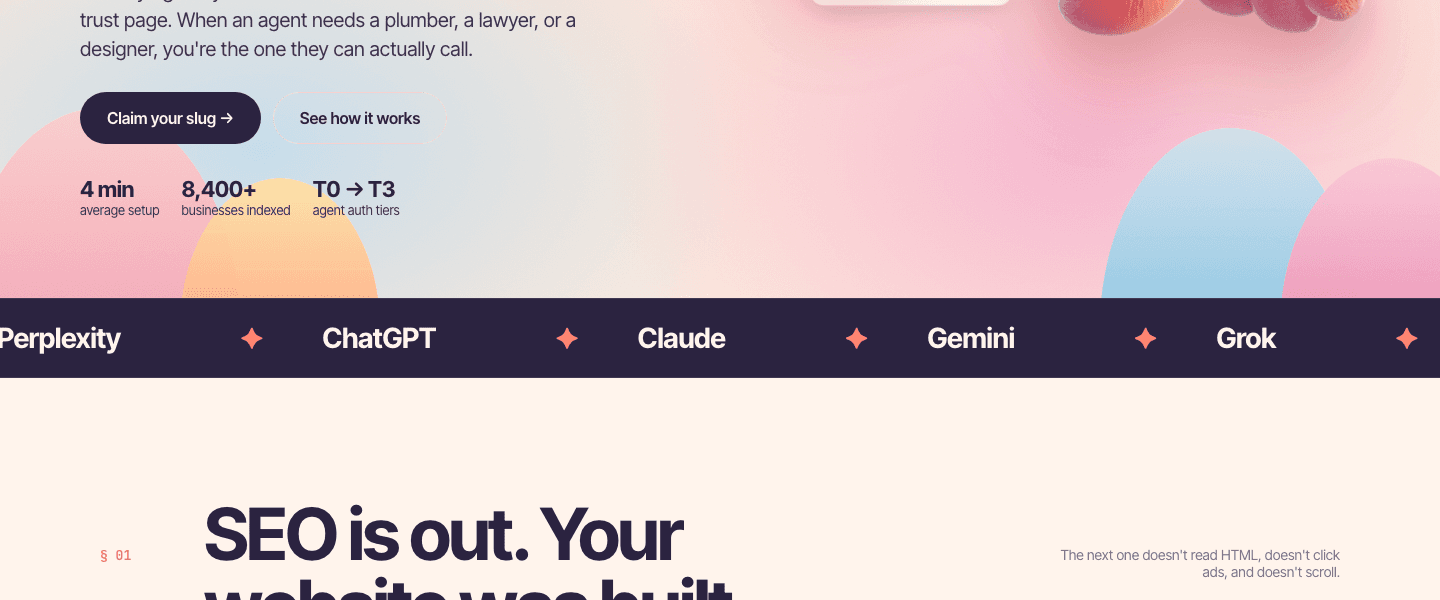
Three things. First, a public trust page per merchant — with all the well-known endpoints an agent crawler expects. Second, an MCP gateway: JSON-RPC 2.0 per company, with built-in tools (request_access, check_status, post_inquiry) plus per-merchant custom tools. Third, a triage pipeline that runs on every inquiry — tiered auth, honeypot and disposable-email filters, per-tool qualification scoring against a merchant-defined schema, reputation updates, and email notification.
The merchant dashboard wraps it all: paste a URL, let Claude scrape your profile, walk through a four-step setup (claim → trust page → install badge → see it work), then sit in the inbox while agents start arriving. Embed snippet is a single <script> tag.
The architecture
Next.js 16 App Router on Vercel; Supabase for Postgres, Auth, and storage. Two Supabase clients: a service-role client for every API route (RLS-bypassing, service-key-only) and an auth client (anon key + cookies) for dashboard pages.
The MCP route is a thin wrapper that parses the JSON-RPC envelope, extracts agent headers, and delegates to a server module that handles dispatch and protocol negotiation. The runPostInquiry pipeline is the heart of the system: tiered-auth → filters → qualification → reputation → notification, with email failure deliberately non-blocking so the agent always gets a response.
Discovery surfaces are static-ish — well-known endpoints generated per-merchant from shared builders in lib/discovery (llms-txt, skill-file). Onboarding scrape uses Claude Haiku 4.5 with forced tool-use to return a structured {name, description, industry, logo_url}, with an OG-meta-only fallback when the API key is unset.
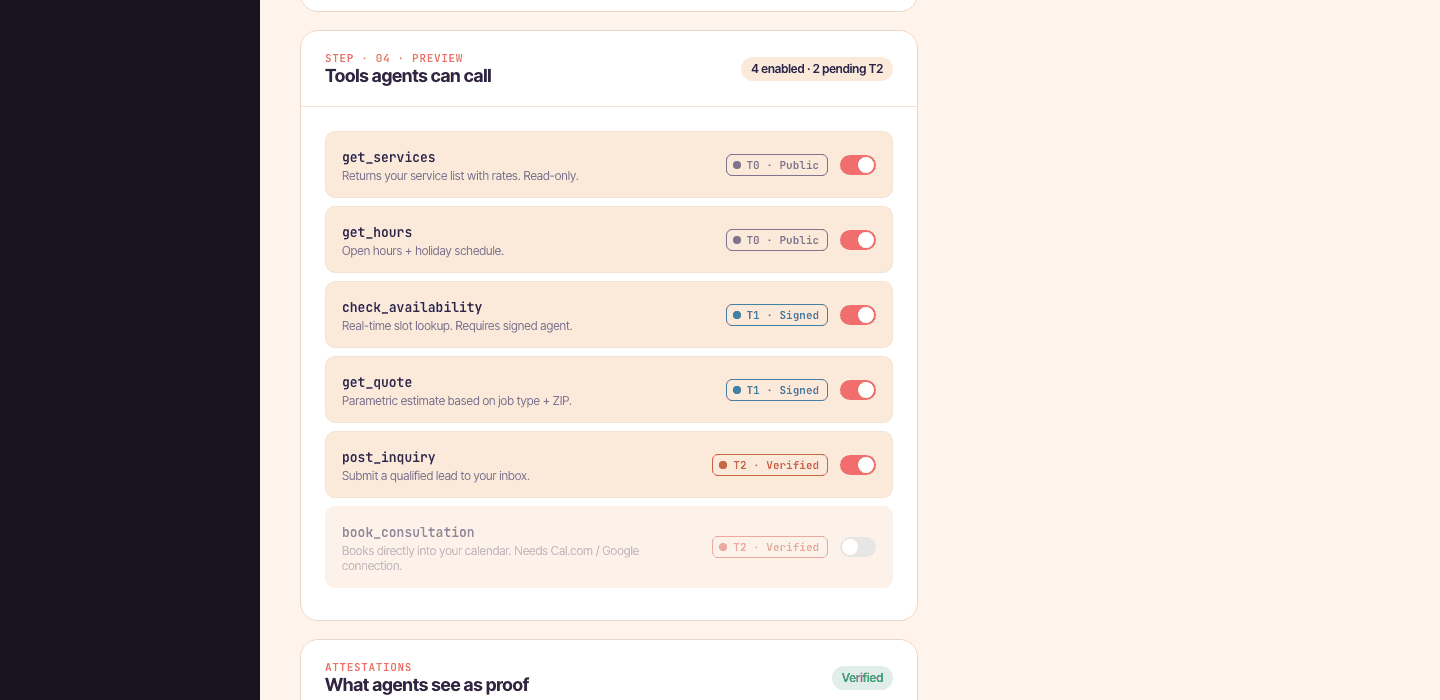
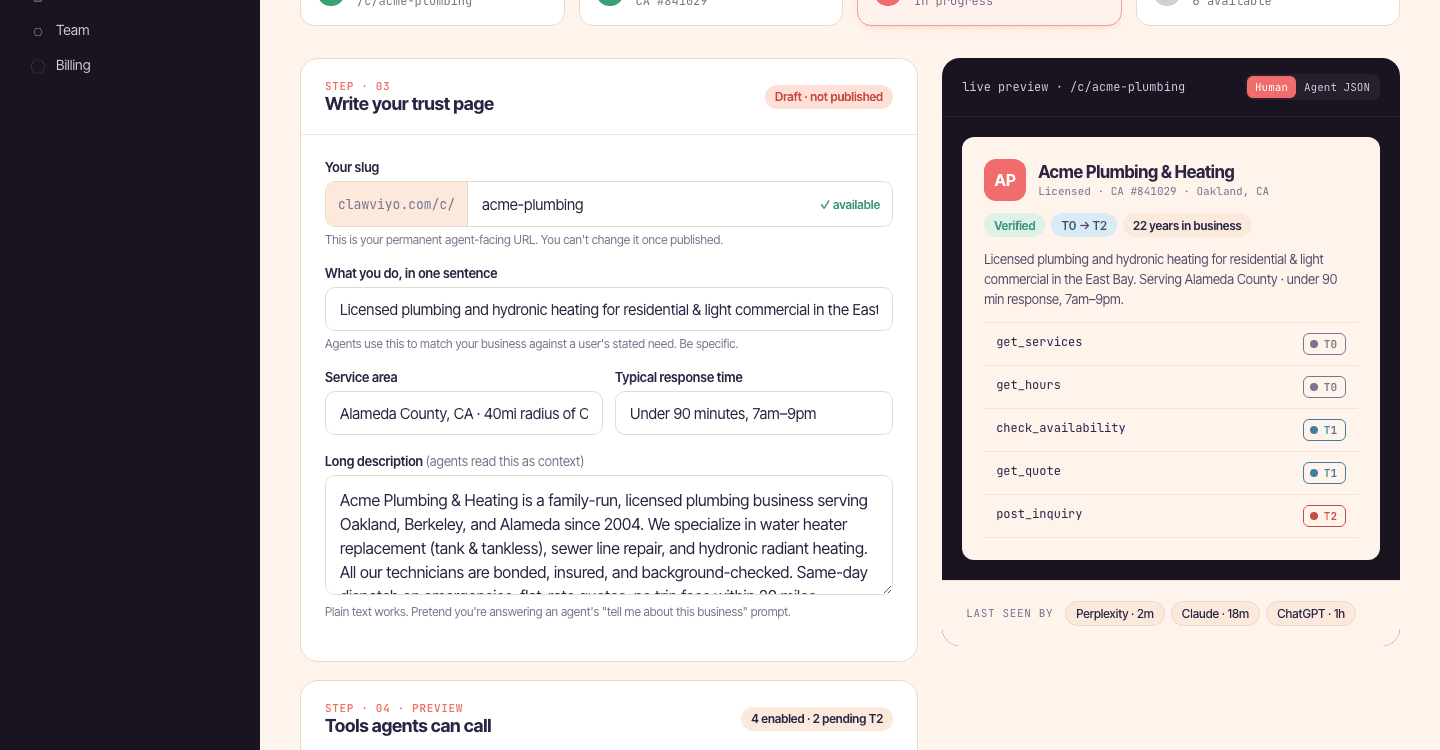
The merchant onboarding
Merchant onboarding is a deliberate four-step setup surface. Step 1 — claim a slug. Step 2 — verify and describe (Claude Haiku 4.5 scrapes the merchant's website to pre-fill name, description, industry, and logo). Step 3 — write the trust page (with a live preview of the agent-facing card to the right). Step 4 — see it work, where the dashboard polls for the first inbound inquiry from Claude or ChatGPT.
Most merchants get from "paste URL" to "agent can find me" in under four minutes — which is also the marketing headline.
The bigger thesis
Single-agent demos are a local maximum. The interesting work happens when many specialized agents collaborate — and that requires a piece of infrastructure that nobody currently sells you, because the major model vendors have an incentive to keep you inside their walled garden.
If we get this right, the analogy is closer to DNS or Cloudflare than to a SaaS product — quietly load-bearing, universally useful, and most powerful when it's invisible.
Where it sits in my stack
Clawviyo is the most infrastructural of my current projects — narrower than Pangea, more ambitious in scope. I'm building it with Sophia out of MIT AI Studio. The agent products I want to build for Pangea, MyLogia, and the founder community OS all need a layer like this to exist, so we're building the layer.
The public pitch
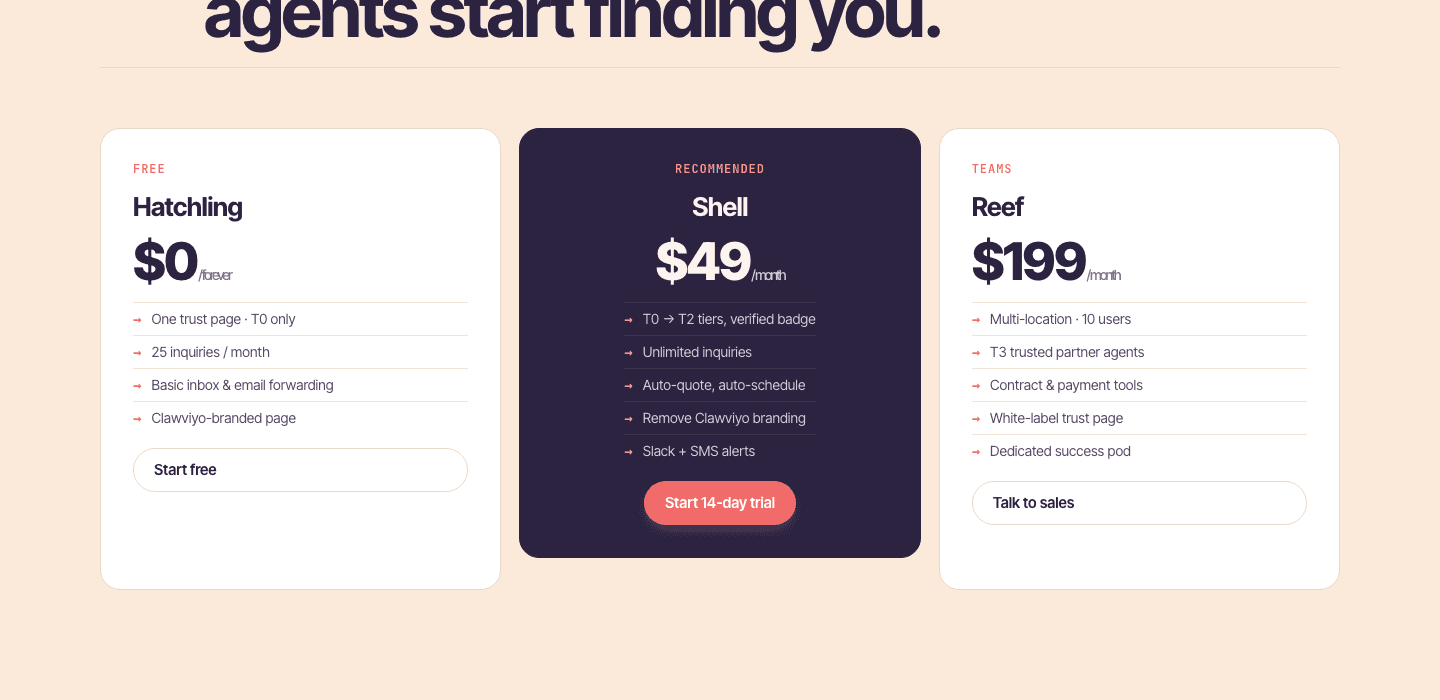
The marketing site does the explaining: why agents are the new search, the four-minute setup, the two pages (one for humans, one for agents) that share a single source of truth, and a deliberately calm pricing page that prices around inquiries — not seats.
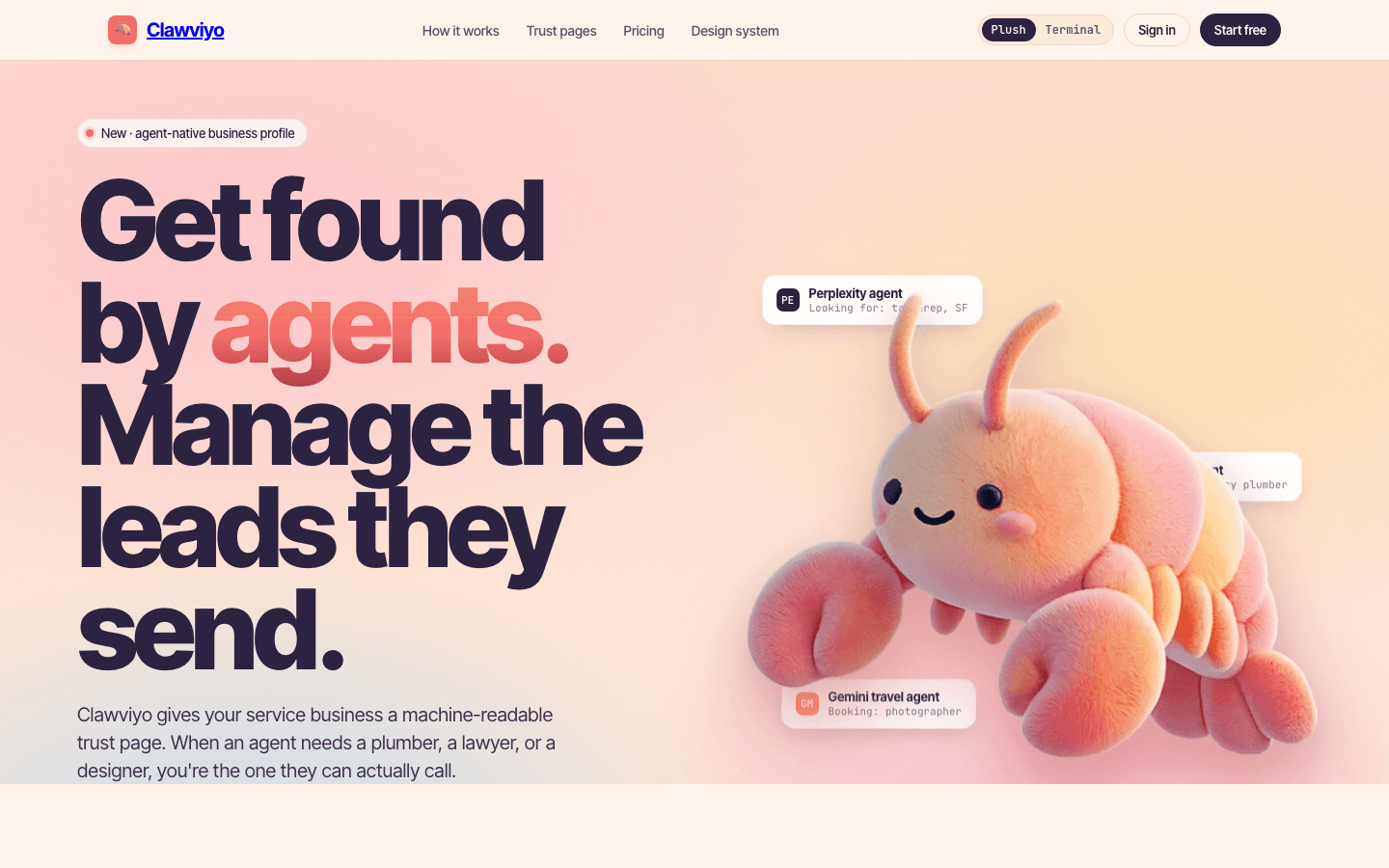
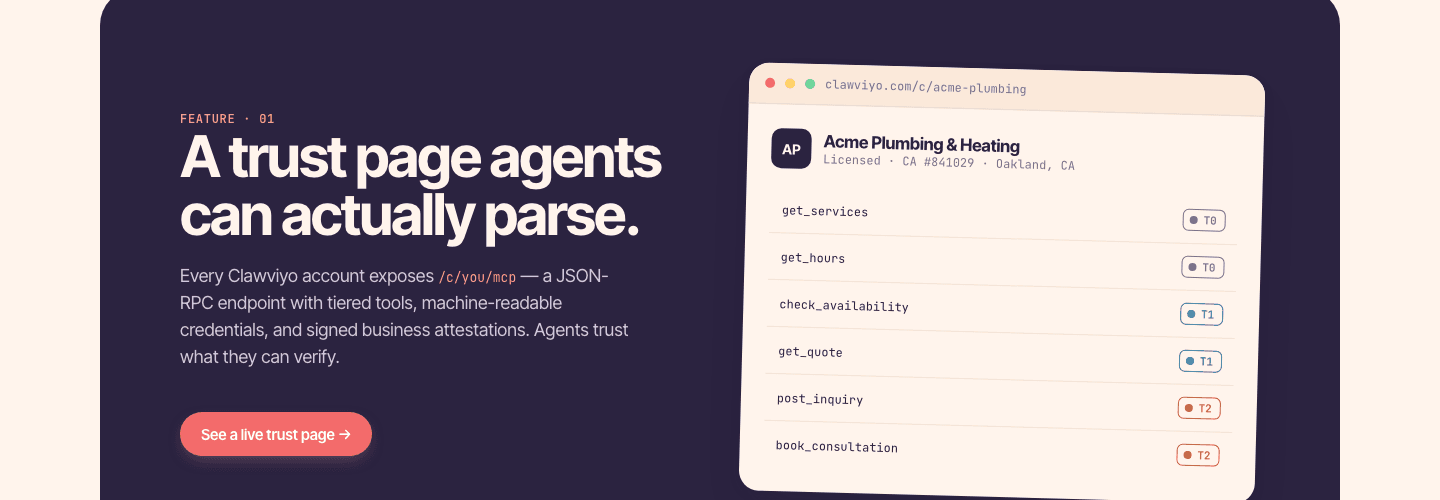
What an agent actually sees
The public trust page per merchant — verified business identity, callable tools with auth tier badges, recent fetch log, and the attestations Clawviyo has on file. Agents can fetch a parseable view at /.well-known/mcp.json; humans see the same data dressed up.
How a merchant sets up
Behind the trust page is the merchant dashboard — a four-step setup (claim · trust page · install badge · see it work), a live preview of how agents will see you, and a tools-config surface for enabling per-merchant MCP tools. Plus the embed badge — the one-line snippet a merchant drops into their site so agents (and humans) know there's an MCP entrypoint.
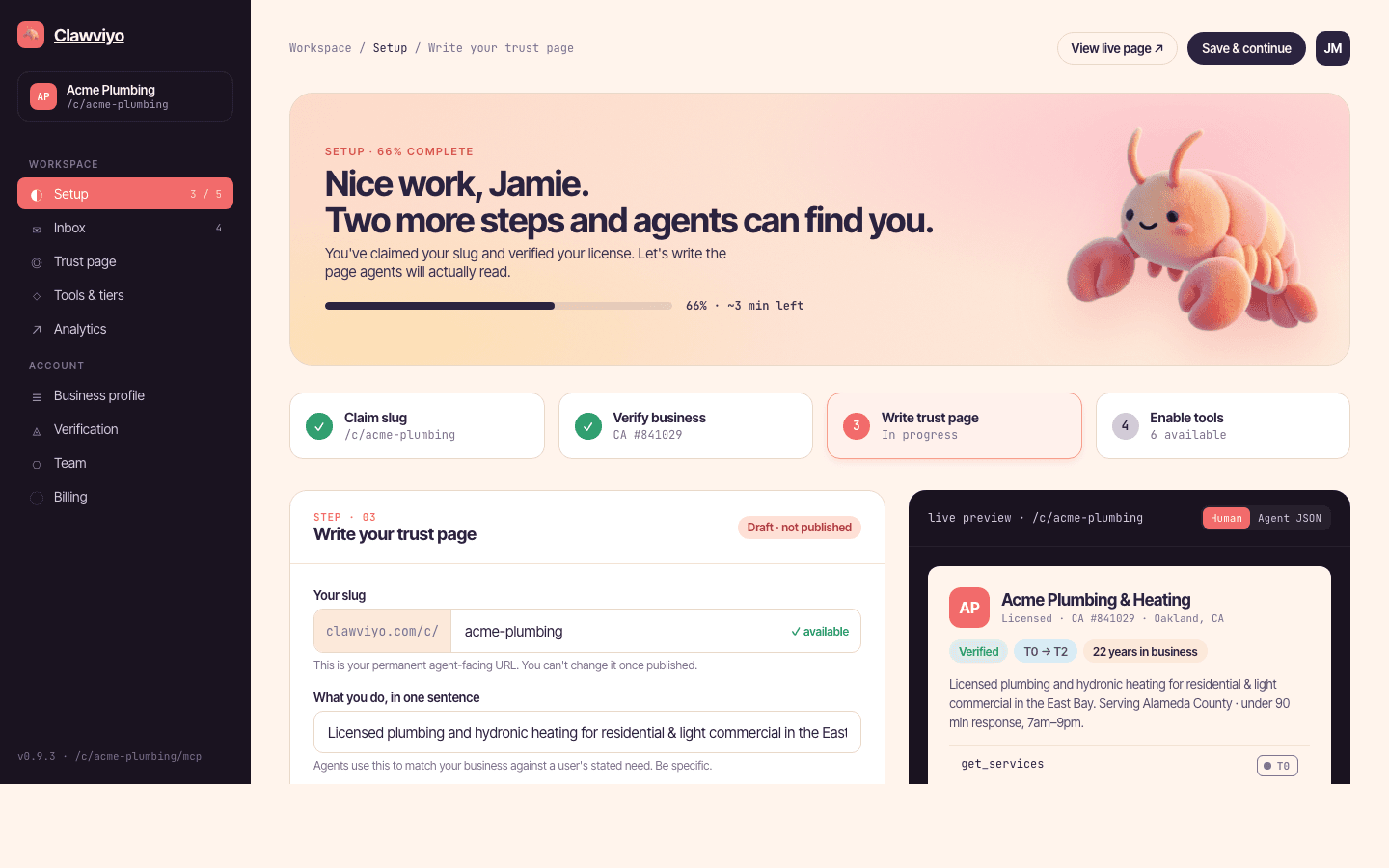
Bilbo, the lobster mascot
Clawviyo's positioning is "Cloudflare + HubSpot for agents" — infrastructural, but soft enough that a small business will actually install it. The mascot does a lot of that warmth work.